On July 7, 2022, the US Attorney for the Northern District of Texas announced that Ping Express had been found guilty. Prior to this, their CEO Anslem Oshionebo*, their COO Opeyemi Odeyale (now imprisoned at the Danbury Federal Correctional Institute, 60177-177), their IT Manager Aleoghena Okhumale (now imprisoned at the Fort Worth FMC), and Olufemi Sadiq (now imprisoned at the Pollock FCI) were arrested on March 10, 2020.

What was Ping Express? Ping was a small business, never having more than ten employees, which operated from 8585 N. Stemmons Freeway, Dallas, Texas. Their CEO was Anslem Oshionebo and their COO was Opeyemi Odeyale. Ping had a smart phone app and a website and advertised that its users could easily send money to Nigeria for a small fee. It operated by having money on deposit in Nigeria. When a US-based client requested a transfer, a hold was placed on the customer's bank account (similar to a hold placed when one rents a car or stays in a hotel.) Then Ping would transfer funds from its Africa-based wallet to the recipient's Africa-based bank account. When the transfer was completed, Ping would then request payment from the sender's bank account.
While this post is about the US-based aspects of Ping Express and their crimes, the company's Instagram page continues to advertise that individuals in many places can use their services, including the UK, Canada, and Europe.
During a three-year period examined in this case, Ping transferred more than 300,000 payments totaling $167 Million USD. During this time it did not file a single Suspicious Activity Report, although they did make some batches of reports under section 5318(g) in 2015, 2016, and 2019.
To maintain a business license in Texas, they were required to file a detailed business plan, including their statements regarding how they would comply with BSA/AML laws (Bank Secrecy Act and Anti-Money Laundering Act, including CFT, Countering Financing Terrorism). Among the rules that Ping established and conveyed to the state of Texas, they agreed to the following:
- All first-time customer transactions are limited to $499.
- Total monthly transactions cannot exceed $4500.
- Further transactions are limited to $1800 each, with a $3000 daily maximum.
They also claimed that they had "automated velocity checks" and the ability to "track and block IP addresses" to help prevent violations.
The court records include a "Factual Resume" "in support of Ping Express US LLC's plea of guilty to the offense in Counts 1 and 2 of the Superseding Information."
Count One - "failure to maintain an effective anti-money laundering program" was proven by demonstrating the defendant acted willfully in failing to develop, implement, and maintain an effective anti-money laundering program.
Count Two - "operating an Unlicensed Money Transmitting Business"
In the Factual Resume, the Count One requirements which they failed to implement are stated as:
An "effective anti-money laundering program" which is required by law, requires that Ping Express establish one or more of the following minimal requirements set forth by regulations of the Secretary of the Treasury. The Guilty Plea confirms that they failed to do so:
a. Effective written policies, procedures and internal controls for one or more of the following:
i. Verifying customer identification
ii. Filing reports, such as suspicious activity reports
iii. Creating and retaining records
b. Designating a person to assure day-to-day compliance with the anti-money laundering program, including assuring that:
i. Ping properly filed reports, created and retained records, in accordance with applicable requirements, such as suspicious activity reports
ii. the [AML] program was updated as necessary to reflect new requirements
c. Provide education and/or training of appropriate personnel concerning their responsibilities.
Examples of AML Failures
Many specific examples are then listed, demonstrating the failures of Count One enforcement, in the Factual Resumes for Ping itself, and also for its CEO and COO who have also both pled guilty:
- Fatai Okunola, a first-time customer, sent $1800 in January 2018
- Raman Saliu, a first-time customer, sent $1800 in October 2017
- Jeffersonking Anyanwu, a first-time customer, sent $1400 in March 2018
Between April 1, 2016 and June 30, 2018, 1500 different customers violated the maximum monthly transfer rules.
Okunola sent more than $6700 his first month, and broke the $4500 rule every month from January 2018 to November 2018. He sent $80,000 just in August 2018!
Anyanwu paid $17,000 through Ping, and broke the maximum monthly rule six times between March and November 2018, paying more than $10,000 in a month four times.
Another customer broke the rule six times from October 2016 through June 2018.
Okhumale, who worked for Ping as their IT and Technical Support Manager, broke the monthly rule three times, paying $25,000 just in October 2018.
The daily rule was also largely ignored. Okunola violated the $3000 daily limit 45 times, and sent more than $5000 in a day 20 times! Okhumale, the Ping employee, sent on three consecutive days in October 2018 $4600, $5200, and $3600! Collins Orogun sent more than $3000 per day 60 times between November 2018 and December 2019, totaling more than $300,000!
Although Ping claimed that they used the IP address of the customer to ensure that they lived in a state where Ping was licensed to do business, and required customers to submit a utility bill from a company where they were licensed to do business as proof of residency in that state, they frequently ignored this rule. Ping was only licensed to do business in Georgia, Maryland, Texas, Washington State, and Washington D.C.
- Joseph Kadiri, a Ping customer, sent $216,000 claiming to be in Texas or Maryland, when in fact he resided in New York and Michigan where Ping is not licensed. He violated the daily limit 20 times and the monthly limit twice.
- Isaac Omohake, a Florida resident, sent $469,000 through Ping, which is not licensed in Florida. He violated the daily limit repeatedly, and in November 2018 sent $78,000 in one month.
- Taiwo Akinsanmiju, an Indiana resident, started sending funds at age 17 (a violation) and sent $220,000 to 85 different named individuals!
- Ayodeji Jegede, an Ohio resident, sent $468,000 through Ping, violating the first transaction rule, the monthly rule (twelve times from June 2018 to June 2019) and in May 2019 sent $69,000 in a single month!
Investigators found that Ping's top 100 customers sent $19,400,000 from March 2016 through September 2019, and that 2/3rds of these customers were from "unlicensed" jurisdictions. Ping was fully aware that these customers lived in unlicensed states. When the Ping offices were search on March 9, 2020, 130 customer shipping labels were found for statements being sent to unlicensed states. Just those customer's transactions were $4,000,000!
The laws in this area are United States Federal Code Title 18 Section 1956, the Anti-Money Laundering Law, and Title 18 Section 1960, the Prohibition of Unlicensed Money Transmitting Business Law. The first states that you may not process funds that you know or should know are derived from certain specified criminal activities. (There are 200 such illegal activities specified in the law.) It specifically states that you cannot allow yourself to be "Willfully blind" to the source of funds. Detailed guidance, often called "Know Your Customer" or KYC, is provided for how to recognize and report suspicious activities.
As examples of transactions from unlicensed states, Ping processed for residents of:
- Nevada: $476,000
- New Jersey: $234,000
- Utah: $1,500,000
- West Virginia: $507,000
- Connecticut: $626,000
When a customer entered their street address at registration, Ping willfully chose to not include the City, State, or ZIP code in their records if the customer was not in a licensed location, storing only their street address.
Ping's Execs and Investors
Ping's Chief Operating Officer, Opeyemi Odeyale, was well aware of US banking law. Prior to Ping, Odeyale earned an MBA from Edinburgh School of Business and held jobs at Pricewaterhouse Coopers, JPMorgan Chase, Oceanic Capital, BNP Paribas, and Barclay's Bank.
During the time he was running Ping Express in the United States, he also served as a director in the British firm "PayZen Limited" from 25JUN2013 through 03DEC2020 (recall he was arrested in March 2020.) His fellow officers at PayZen included Adekanmi Olaolu Adedire and Anslem Oshionebo (Financial Consultant), his CEO at Ping. Notably, Payzen was originally incorporated as Fiem Ltd but changed its name on 10FEB2020. Texas records also indicate that Ping Express originally operated as Fiem Group, LLC, and bank accounts in the name of Fiem Group are on the Forfeitures list below! On 01FEB2017 Opeyemi Odeyale filed papers with Companies House indicated that his nationality had changed to "British." When the British company was first incorporated (as Clicks FX Limited), he had given his date of birth as 14FEB1979 and his nationality as Nigerian.
Ping's Chief Executive Officer, Anslem Oshionebo, began his career with an MBA from Seton Hall University's Stillman School of Business. His LinkedIn page says he worked at PriceWaterhouse Coopers for 14 years, working his way from Senior Associate to Manager, and then Senior Manager, at least partially in Los Angeles. He then worked at Riveron Consulting as a Principal in the Dallas/Fort Worth area before co-founding Ping Express in 2014. His Crunchbase profile says that his areas of practice at PWS included "Compliance regulations and financial forensics!" Anslem's domain "anslemoshionebo.net" has articles he has written on philanthropy and diversity, while his anslemoshionebo.medium.com page has articles about what books Entrepreneurs should read and a five part series called "Challeges of an Immigrant" (which were mostly written AFTER he was arrested!)
In April of 2017, Synergy Capital Managers, a Mauritius-based private equity firm, made an investment in Northstar Finance Services Limited, "a financial services platform providing solutions across the financial service value chain in select countries across West Africa." Northstar was said to be managed by Obafami Alonge and Bolanle Oduyale, In Synergy's announcement, Northstar's CEO said that with this investment the company now had a "majority stake" in Safetrust Nigeria, Northstar Home Finance, Avance Insurance, Ping Express Inc., and Fast Credit Limited. PWC, where Oshionebo worked for so long, was said to be the advisor to Synergy Capital "on Financials and Tax due diligence."
This comes to play in that if Ping had "foreign investors" they are required to disclose those. When the Texas Director of Banking gave the license, they claimed to be based entirely in Texas.
Top Customer: Collins Orogun, Romance Scammer and Money Launderer
Collins Orogun, a Texas resident, paid Ping more than $800,000 which included $220,000 in wire transfers during a six-month period in 2019. Ping only reported $292,500 of these transmissions. (Collins was released from prison on 12MAR2020 for prior charges but has another sentencing hearing in October 2022 for the current charges.) In his guilty plea, Orogun admitted that he received funds from people "all across the United States" in forms including cash, money orders and checks. He then deposited those funds into his accounts, including at JPMorgan Chase, both in his true name and as "Collins Enterprise", at Navy Federal Credit Union, at Wells Fargo Bank, both in his true name and as Orogun Enterprises, and at BBVA.
His JPMC accounts received $120,000 in funds, which he sent out through Ping in 13 transactions. In another example, he received $26,500 "in currency and money orders" between November 29, 219 and December 31, 2019. He sent these funds out via Ping in six $5,000 transactions. In his Navy FCU account, he received $530,500 in "currency and money orders" and sent a wire transfer of $218,500 out. He also sent $192,600 via Ping in 68 transactions. His first Wells account received $87,171 in deposits, sending $65,610.56 of those out via Ping. His second Wells account received $157,578 in deposits, of which he sent $82,367 out via Ping. His BBVA account received $144,808 in deposits, of which $140,000 was sent out via Ping.
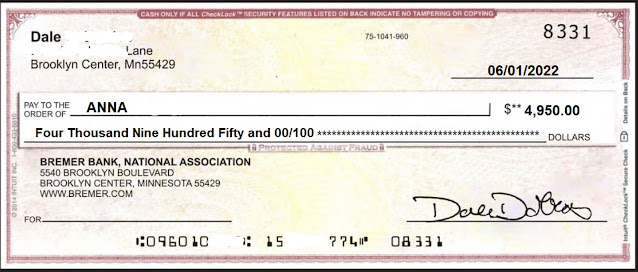
Some of his Romance Scam victims included:
$40,000 into BBVA that came from "D.M." a senior citizen in California who sent the money to facilitate the sale of an estate in Nigeria. He believed that he was helping to repair an estate which would be then sold for $570,000,000, and that he would receive a large repayment when the estate was sold.
"P.L" from Indiana believed her $6,309 was sent to "Thomas Ken" an Irish sea captain with whom she had a romantic online relationship. The funds were supposed to be used to repair his ship. She took out a title loan against her vehicle and wired the money to Orogun Enterprises. The captain immediately asked for more funds afterwards.
"D.N." a 59 year old in Indiana sent $2300 to the BBVA acount, believing that "Carson Steve Jacks" an oil roughneck working in the Gulf of Mexico needed the funds because he had contracted malaria and couldn't work. He later asked for an additional $15,000. The couple "fell in love" via Google Hangouts.
These three had all agreed to testify at trial, prior to Collins changing his plea to Guilty on June 28, 2022.
Additional Factors Violating Texas Department of Banking License
The Texas Department of Banking found many more reasons for considering revoking Ping's business license, including:
- Ping stated that they had no "authorized delegates or agents" yet Nimerex claims to be Ping's agent and has Ping letterhead documentation appointing them as Ping's agent.
- Ping claimed to have no foreign affiliates, but had received $160,000 from a Mauritius-based account in the name "Ping Express (Mauritius) Ltd." "for the benefit of Fiem Group LLC" and a $280,000 wire from a British account in the name Ping Express CM.
- Ping claimed to be sending "small remittances" back to Nigeria, but had sent $1,600,000 in large round number wire transfers to business bank accounts in Nigeria (at First City Monument Bank and Wema) for "marketing" and "consulting" payments.
- Ping received $49,000 in wire transfers from the company "Date2Marry LLC" and an individual connected with that LLC.
These details came out during a search of Olufenwi's phone as he returned to California from England. The phone also documented a five year "currency exchange partnership" between Ping and "Wilfobs Bureau De Exchange Limited" in Nigeria involving multiple foreign bank accounts for Ping. Ping had disclosed in previous reporting to the Texas Department of Banking that they had no bank accounts outside U.S. borders and thus were not required to file a Foreign Bank Account Report.
Chats on Odeyale's phone made it clear he was trying to avoid AML and Suspicious Activity detection as he received foreign funds. An example:
Forfeitures ordered by the Court
Forfeiture Notice:
- Approximately $10,601.52 in funds seized from the JPMorgan Chase Bank
account with number ending in 2885 in the name of Collins Ogaga Orogun.
- Approximately $3,679.78 in funds seized from the JPMorgan Chase Bank
account with number ending in 8900 in the name of Collins Ogaga Orogun dba
Collins Enterprise.
- Approximately $42,873.96 in funds seized from the JPMorgan Chase Bank
account with number ending in 1223 in the name of Ping Express LLC.
- Approximately $1,385.13 in funds seized from the JPMorgan Chase Bank
account with number ending in 2686 in the name of Ping Express LLC.
- Approximately $13,269.69 in funds seized from the JPMorgan Chase Bank
account with number ending in 5397 in the name of Crusaders Health and
Wellness LLC.
- Approximately $3,010.72 in funds seized from the Navy Federal account with
number ending in 2248 in the name of Collins O Orogun.
- Approximately $8,307.53 in funds seized from the Wells Fargo Bank account
with number ending in 4593 in the name of Anslem Oshionebo.
- Approximately $369.82 in funds seized from the Wells Fargo Bank account
with number ending in 4437 in the name of Blackbit LLC.
- Approximately $8,364.86 in funds seized from the Kasasa Tunes 0031 account
at Neighborhood Credit Union for member number XXXX5691.
- Approximately $55,235.41 in funds seized from the Soho Business Checking
account at Resource One Credit Union for member XXX1450 in the name of
Fiem Group LLC.
- Approximately $37.40 in funds seized from the Bank of America account with
number ending in 3918 in the name of Deyks LLC.
- Approximately $9.91 in funds seized from the Bank of America account with
number ending in 3921 in the name of Deyks LLC.
- Approximately $14.15 in funds seized from the Bank of America account with
number ending in 3947 in the name of Deyks LLC.
- Approximately $11.52 in funds seized from the Bank of America account with
number ending in 3692 in the name of Deyks LLC.
- Approximately $29,198.23 in funds seized from the Capital One account with
number ending in 2957 in the name of Aleoghena Okhumale.
- All funds seized from the account with number ending in 1891 at Silvergate
Bank in the name of Wyre Payments Inc. deposited after February 19, 2020
from “5/3 BANKCARD SYS DEPOSIT; 5/3 BANKCARD; or WORLDPAY”.
* - (Although Anslem was to surrender to be imprisoned on July 12, 2022, the Federal Bureau of Prisons Inmate Locator indicates he is not currently in custody.)