Have you ever seen those spam messages claiming they have a great job for you as a Mystery Shopper? After seizing a check from a client (and then shredding it) a local bank let us check out the scam! In this scam, a company claiming to be "Private Mart Auditors" says they have been contracted by WalMart to try to identify stores that are violating their policies by refusing to sell Gift Cards! The project claims to actually be a partnership with the gift card companies themselves and the major retailers who sell them.

The criminals know that many companies have trained their personnel that if someone comes in and says "I'd like to buy $2,000 worth of Gift Cards!" they should ask probing questions to try to save someone from being scammed. Some companies even have big signs on their registers, check-cashing terminals and gift card sales racks warning about scammers. When we reviewed our Mystery Shopper instructions, we were told to validate our check by visiting their website ==> verifycheckatmet[.]org or verifycheckatbictoin[.]org. (The instructions actually provide both URLs.)
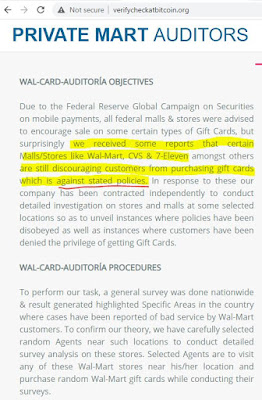
What we learned at the website is that Wal-Mart's Audit Team had contracted our new employer to conduct an audit. We were selected because some of the stores in our area were discouraging people from purchasing gift cards, despite the "Federal Reserve Global Campaign on Securities on Mobile Payments" requiring stores to encourage Gift Card purchases!
We wanted to proceed cautiously, so we validated each of the facts in our instructions just as they requested. A few red flags came up, but these were easily explained by our new supervisor, Paul Newton. Paul sends and receives texts from 574-777-6314 and uses the gmail account paulnewt005@gmail.com.
First question -- why was this package, which claims to be from GNT Solutions at 5201 Thurman Way in Sacramento, California, being mailed through the US Postal Service from the Orlando, Florida area?
Second question -- if they are in Sacramento OR Orlando, why is the routing number on their check used exclusively for TD Bank branches in Maine?
Fortunately, we had an easy way to validate that OUR check was legitimate. If we clicked the "Verify Cheque" button on the website, we could enter our name and check number. If it was a valid check that had been issued by the company, it would instruct us to Proceed with Deposit. If it was NOT a valid check it would tell us so, and instruct us what to do next. So, we carefully entered our information:
And ... we were in luck! The check was totally valid!
According to our instructions, here's what we needed to do next:
1. Cash check or deposit at your Bank, then text your supervisor immediately via 574-777-6314 to receive further instructions.
2. Deduct your Salary $350 while you withdraw $2000 for your assignment.
3. Locate any 2 Wal-Mart stores near you.
4. Visit the first store and purchase 3 Wal-Mart gift card worth $400 each.
5. After purchasing the 3 cards successfully scratch each of the cards to reveal its code, take CLEAR pictures and send to your Supervisor on 574-777-6314.
6. Proceed to the second Wal-Mart store to purchase 2 cards worth $400 each, scratch each & take pictures to be sent to your supervisor.
7. With the help of your supervisor answer questions from the WAL-CARD AUDITORIA EVALUATION FORM then take a picture & sent to your assigned grading personnel via email to paulnewt005@gmail.com
8. Keep the cards safely as they will be used for your second assignment provided you meet the pass mark otherwise you will be mailng them back to an address to be provided by your supervisor.
9. We encourage giving back to the society as such the moment result is sent to email, you are to purchase a Cashier's Check worth $30 at your bank in the name KIDNEY FOUNDATION. After purchase text your supervisor for further instructions on the purchased Cashier's check.
If we pass our "grade" we might be able to become a Permanent Contract employee, where we would earn $450 per assignment and do 3-4 assignments each week! If we do well with that, we might become a "WAL-CARD-AUDITORIA CONTRACT" employee! Then we would earn $600 per assignment and could do MORE than four assignments a week!
Now, if you are an unemployed person due to Covid and someone gives you a clear path to earning $150,000 per year, might you be tempted? Other than our Check, here are the instructions and the PMA Evaluation Form that were also in our US Postal Service Priority Mail package. (Click for full-size)
The Website - and possibly related scams!
Of course we also wanted to look into that website! We used the Zetalytics Zonecruncher tool to check it out. The domain name was registered at Public Domain Registrar, which wasn't shocking. The last APWG report showed that with the exception of cyber criminal's FAVORITE Registrar NameCheap, PDR has recently been the second most common Registrar for BEC attacks, and this scam is definitely related, as we'll see.
It is hosted at 67.220.184.146, and its nameservers, ns5.doveserver.com and ns6.doveserver.com are also located on 67.220.184.146 and .147.
 |
| ZoneCruncher data |
One of my favorite things about ZoneCruncher's data is that it shows the "Start of Authority" record. In this case it is telling us that the reseller to which this IP address space is assigned is "csf@smartweb.com.ng"
One of the most common West African scams, besides the shipping of counterfeit checks, is various "delivery" scams. These started with the earliest Nigerian Prince scams, but more frequently today involve a package of value (a box of diamonds, for example) that a soldier finds overseas and wants to ship to you to sell and split the profits. Other times it is a "pet delivery" scam, where you anticipate having a pet shipped to you and the pet gets caught up in shipping. As anticipated, we had plenty of these on this IP address.
One of the things that all of these sites have in common is a "TRACK Your Package" option. This is where the scammers match pre-assigned tracking numbers to various conditions which require your payment to break a shipment free. Pets may be "quarantine hold in customs" or valuables may be "inspection hold in customs." Your scammer will send the website address with a tracking number so that you can look up "proof" of the situation.
- https://regalcourierservice[.]com/track/
- http://cargoexpedite[.]com/tracking.php
- https://submarinecourierservice[.]com/track-your-shipment.php
- https://www.safecargoeslogistics[.]com/?page_id=3731
Often you can find many websites with identical content but a different company name. Also a red flag. For example:
http://ftcouriercompany[.]com/about.html (hosted on "our" IP address)
http://logitrex[.]net/about.html (hosted on 104.194.9.169, which leads to a whole new cluster of badness:
==> https://wpsdelivery[.]com/
==> https://nexaglobalexp[.]com/tracking.html
==> https://aimsair-ways[.]com/