Today I saw a tweet quoting Mark Guzdial's blog saying "In last five years, little progress in increasing the fraction of American CS BS degree recipients who are African Americans." It is a problem I've given quite a bit of thought to, but in my thinking, diversity is a problem I approached from another angle. I've always been pleased that a large number of women have decided to work on the problems I care about. When I came to the University of Alabama at Birmingham (UAB) I didn't come to "teach Computer Science." I came to try to change the way we train, recruit, and equip cyber crime fighters. I was fortunate that our department chairs in Computer Science (Anthony Skjellum) and Justice Sciences (John Sloan) believed that was something worth doing. Since then, we've moved from having a certificate in Computer Forensics, to a Masters in Computer Forensics and Security Management, to a full Bachelors degree in Digital Forensics. But the passion has stayed the same. How do we train, recruit, and equip cyber crime fighters?
I hadn't realized that we were necessarily doing something unique until I had a visit from Jenn Lesser in April of 2013. At the time, Jenn was the Security Operations Manager for Facebook. We had a full agenda of things we were hoping to discuss with her, but something happened that halted all of that. She came into my office, closed the door, and said "You have SIX WOMEN working in your lab! Would you mind if we cancel everything else and just let me interview them?" At the time my lab was much smaller and that represented about 1/3rd of my employees. What Jenn learned was that most of the women in the lab were there because they wanted to fight crime, right wrongs, and serve the cause of Justice. When they realized that learning to program and analyze hard drives, network traffic, and email headers could help serve that cause better, they were all in.
This fall, I'll have interactions with 83 students in the classroom and 28 of them are women. 11 of the 48 people on my lab payroll today are women, and I hope we'll hire several more at our job fair later this week! I should note that these are not "Computer Science" courses, but rather Computer Forensics courses being taught for Criminal Justice credit.
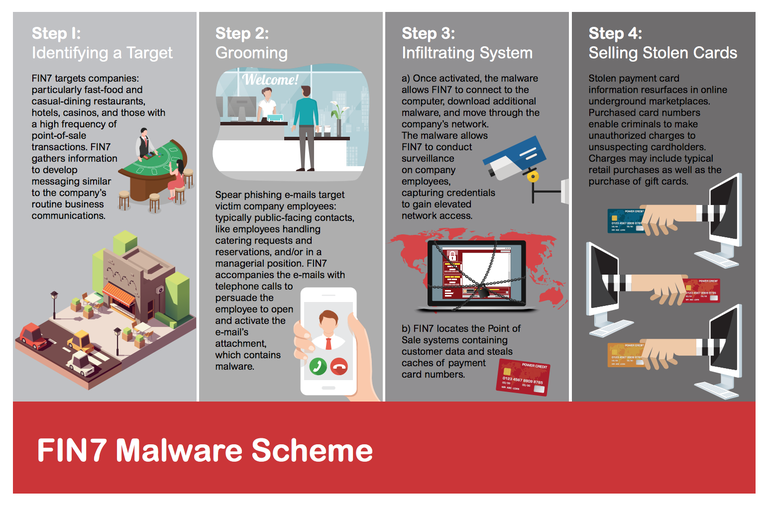
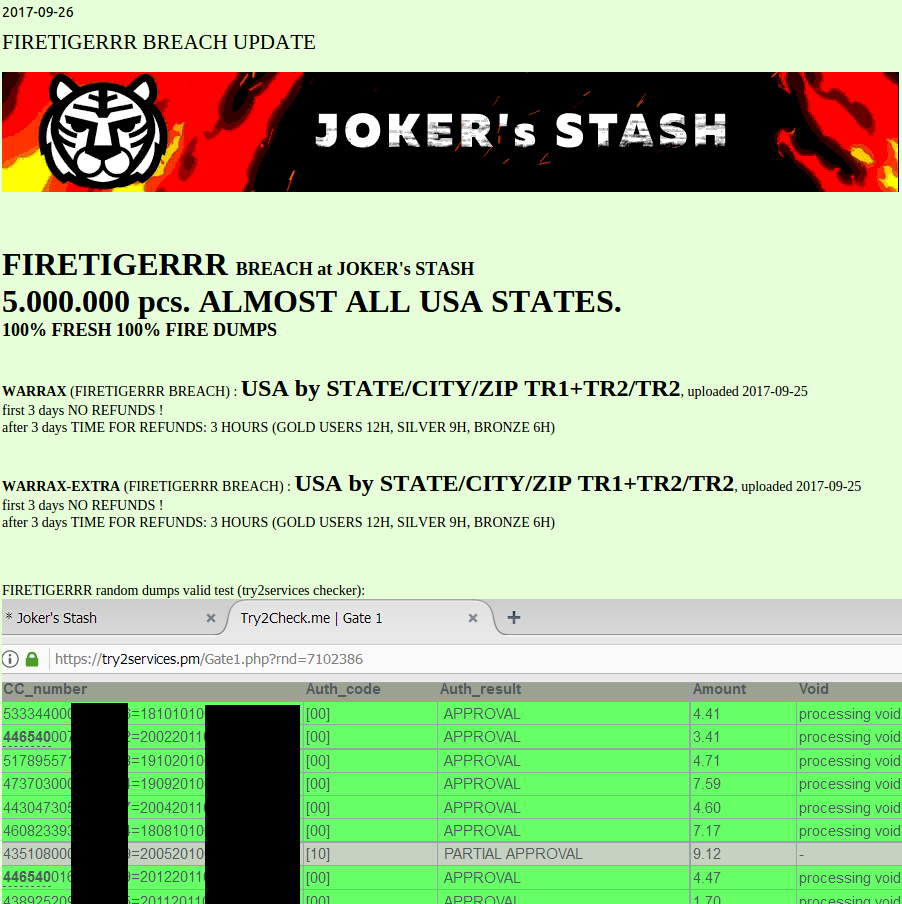
How do we recruit women? It's the same as what our ladies told Jenn Lesser back in 2013. None of them come to our program because they want to write code. They come because they want to dedicate themselves to the cause of Justice, and they have learned, perhaps in an introductory course from myself or my colleague Arsh Arora, or perhaps in an introductory course from Criminal Justice professor Martha Earwood, that being skilled in technology is a force multiplier. If you want to protect the financial assets of the elderly, technology helps. If you want to identify and stop child predators and human traffickers, technology helps. If you want to fight against hate speech on the Internet or cyber bullying in the schools, technology helps. If you want to identify and stop the malware that it is stealing our data, finances, and intellectual property, technology helps.
As I was reading through Guzdial's blog post and following the linked stories, I read Kenneth Bowman's post on African American Computer Science enrollment, and also the 2017 Taulbee Survey on Computer Science Enrollment from the Computer Research Association.
The Taulbee survey has some stark numbers for US Citizen, Female, and African American enrollment in Computer Science at all levels.
Of 12,689 PhD students currently studying Computer Science in 135 departments, 8,058 (64.3%) are non-resident aliens, 2,734 (21.1%) are female, and 170 are African American.
Of the 25,126 currently enrolled Masters students in Computer Science, 16,414 are non-resident aliens. Of the 6,682 females, 5,183 are non-resident aliens. Of the 1,499 resident females, 661 are White, 620 Asian, 95 Hispanic, and 81 Black.
Of the 86,569 students currently enrolled in Computer Science Bachelor's programs, 10,704 were non-resident aliens. Of the 75,865 citizens in CS BS programs, 13,358 (17.6%) were female. By ethnicity, 39,416 (51.9%) were White, 21,113 (27.8%) were Asian, 8,395 (11%) were Hispanic, and 3800 (5%) were Black.
Instead of asking "How to we get more women (or blacks) to study Computer Science?" Perhaps we should be asking "How can we learn what women (and blacks) want to make their life's work and show them how Computer Science can help make them do their life's work better?"
I hadn't realized that we were necessarily doing something unique until I had a visit from Jenn Lesser in April of 2013. At the time, Jenn was the Security Operations Manager for Facebook. We had a full agenda of things we were hoping to discuss with her, but something happened that halted all of that. She came into my office, closed the door, and said "You have SIX WOMEN working in your lab! Would you mind if we cancel everything else and just let me interview them?" At the time my lab was much smaller and that represented about 1/3rd of my employees. What Jenn learned was that most of the women in the lab were there because they wanted to fight crime, right wrongs, and serve the cause of Justice. When they realized that learning to program and analyze hard drives, network traffic, and email headers could help serve that cause better, they were all in.
This fall, I'll have interactions with 83 students in the classroom and 28 of them are women. 11 of the 48 people on my lab payroll today are women, and I hope we'll hire several more at our job fair later this week! I should note that these are not "Computer Science" courses, but rather Computer Forensics courses being taught for Criminal Justice credit.
How do we recruit women? It's the same as what our ladies told Jenn Lesser back in 2013. None of them come to our program because they want to write code. They come because they want to dedicate themselves to the cause of Justice, and they have learned, perhaps in an introductory course from myself or my colleague Arsh Arora, or perhaps in an introductory course from Criminal Justice professor Martha Earwood, that being skilled in technology is a force multiplier. If you want to protect the financial assets of the elderly, technology helps. If you want to identify and stop child predators and human traffickers, technology helps. If you want to fight against hate speech on the Internet or cyber bullying in the schools, technology helps. If you want to identify and stop the malware that it is stealing our data, finances, and intellectual property, technology helps.
As I was reading through Guzdial's blog post and following the linked stories, I read Kenneth Bowman's post on African American Computer Science enrollment, and also the 2017 Taulbee Survey on Computer Science Enrollment from the Computer Research Association.
The Taulbee survey has some stark numbers for US Citizen, Female, and African American enrollment in Computer Science at all levels.
At the PhD Level
In the US and Canada, they found 124 Computer Science departments awarded 1,557 PhDs. 891 went to "non-resident aliens." 291 went to Females. 10 went to African Americans. Of the 291 females, 164 were non-resident aliens. Of the American females, 64 were White, 27 Asian, 4 Black, and 2 Hispanic.Of 12,689 PhD students currently studying Computer Science in 135 departments, 8,058 (64.3%) are non-resident aliens, 2,734 (21.1%) are female, and 170 are African American.
What about Masters Level?
132 US Computer Science departments awarded 12,483 Masters degrees last year. 8,813 (73.8%) are non-resident aliens. 26.1% of those students who reported a gender were female (3,162 females and 8,956 males). 111 (0.9%) of the students were Black. Of the 3,162 females, 2,462 (81%) were non-resident aliens. Of the American females, 272 were Asian, 250 were White, 32 were Hispanic, and 24 were Black.Of the 25,126 currently enrolled Masters students in Computer Science, 16,414 are non-resident aliens. Of the 6,682 females, 5,183 are non-resident aliens. Of the 1,499 resident females, 661 are White, 620 Asian, 95 Hispanic, and 81 Black.
And at the Bachelor's Level?
131 reporting US Computer Science departments awarded 19,907 Bachelors degrees last year. At the Bachelor's level, we have a much greater percentage of American students. Only 12.5% of these were non-resident aliens. But of those remaining 15,433 students, only 547 were Black. Of the 3,198 female Bachelor's degrees awarded, 2669 went to Americans women. Of these, 1,110 (35%) were White, 1,104 (35%) were Asian, 200 (6%) were Hispanic, and 93 (3%) were black.Of the 86,569 students currently enrolled in Computer Science Bachelor's programs, 10,704 were non-resident aliens. Of the 75,865 citizens in CS BS programs, 13,358 (17.6%) were female. By ethnicity, 39,416 (51.9%) were White, 21,113 (27.8%) were Asian, 8,395 (11%) were Hispanic, and 3800 (5%) were Black.
The Question
The question that data like this leaves me with is this? Could it be that the lack of interest in Computer Science from women and minorities (especially African Americans) is similar to what I've found in my lab? Perhaps the key to encouraging Computer Science is to look at it rather than a Subject to be studied, but as a Tool to be Mastered to enable the study of something else? Computer Science as a tool (in my case) to improving your ability to help fight for Justice. Computer Science as a tool to improving your ability to fight disease and illness. Computer Science as a tool to improving your ability in economics. Computer Science as a tool to improving your ability to fight poverty.Instead of asking "How to we get more women (or blacks) to study Computer Science?" Perhaps we should be asking "How can we learn what women (and blacks) want to make their life's work and show them how Computer Science can help make them do their life's work better?"